Relativity Data Breach Response

Turn breach data into defensible, notification-ready outputs

From Patchwork Workflows to One Platform
Ditch the spreadsheets, scripts, and point tools. aiR for Data Breach Response transforms your manual, fragmented cyber incident process into a streamlined, accelerated experience, with data breach response software powered by generative AI.
Scope
Securely process and cull incident-related data to focus on the breach-relevant population.
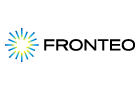
Detect & Link
Automatically identify PI/PHI and connect it to impacted individuals across complex data sets.
Review & Report
Validate edge cases, normalize entities, and generate reviewable outputs ready for notification.
Trusted by Leading Cyber Breach Response and Data Mining Teams
From law firms to service providers, teams rely on aiR for Data Breach Response to reduce manual work, simplify sensitive data mining, and deliver defensible outputs – fast.
 50% improvement in review efficiency
50% improvement in review efficiency
See how Deloitte helped a major retailer meet regulatory deadlines
Learn MoreReport
See how organizations are realizing measurable savings
Learn MoreWhy Firms Choose Relativity for Sensitive Data Mining
One connected workflow in RelativityOne
Scope, detect, link, QC, and export in one platform – without rebuilding work across spreadsheets and point tools.
Defensible by design, empowered by humans
Produce reviewable, traceable outputs that keep human judgment at the center of breach response.
AI-driven sensitive data mining
Go beyond just finding the personally identifiable information (PII) or protected health information (PHI). Detect and link personal information to build consolidated impacted individual profiles and reports faster.
Scale without breaking the workflow
Process broad incident collections, narrow to what matters, and keep everything in one secure environment.
How It Works
Move from analysis to quality control to reporting without recreating work at each stage.
Detect and link data with AI
Automatically identify protected data and link it to affected individuals so reviewers focus on quality control, not manual stitching.
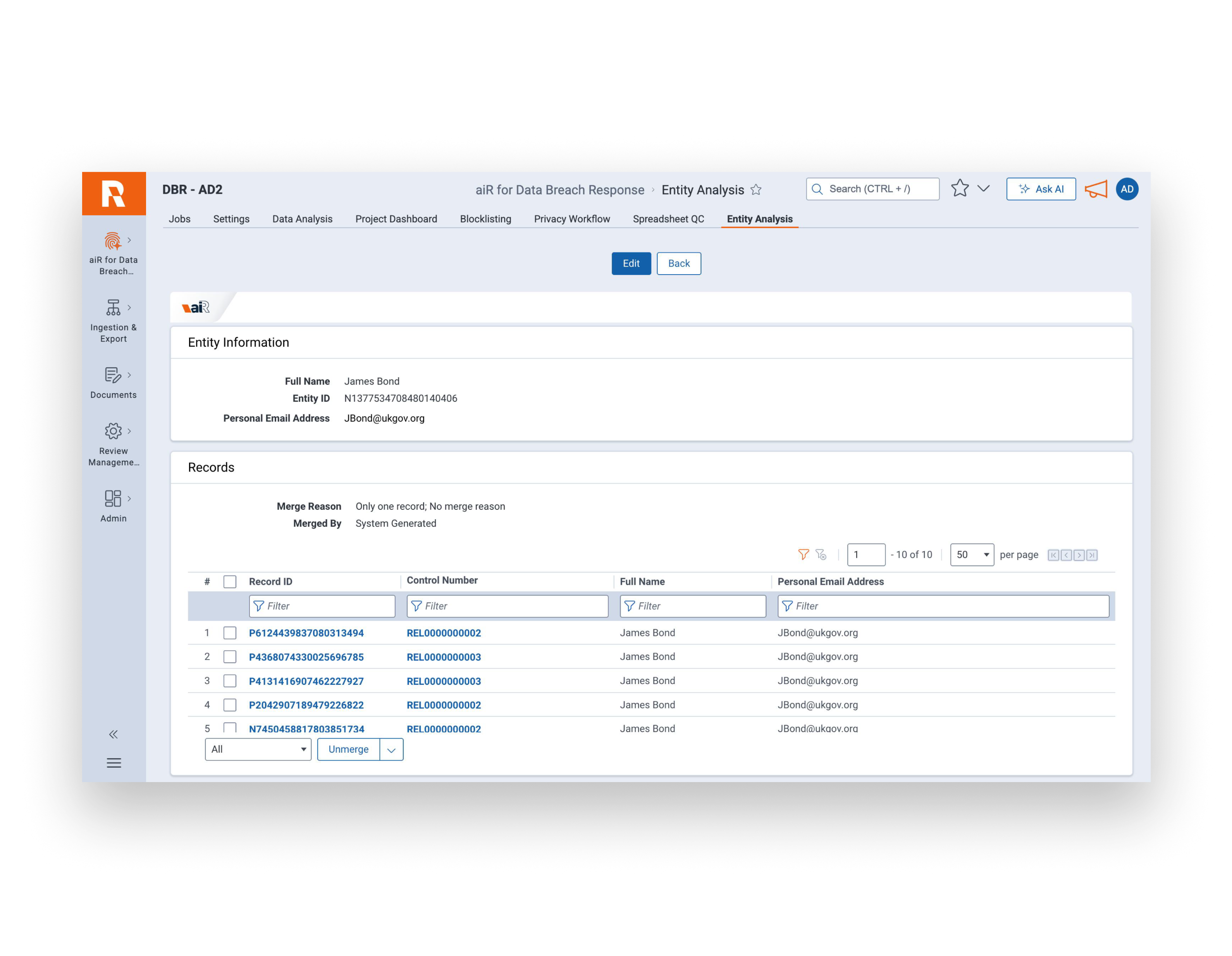
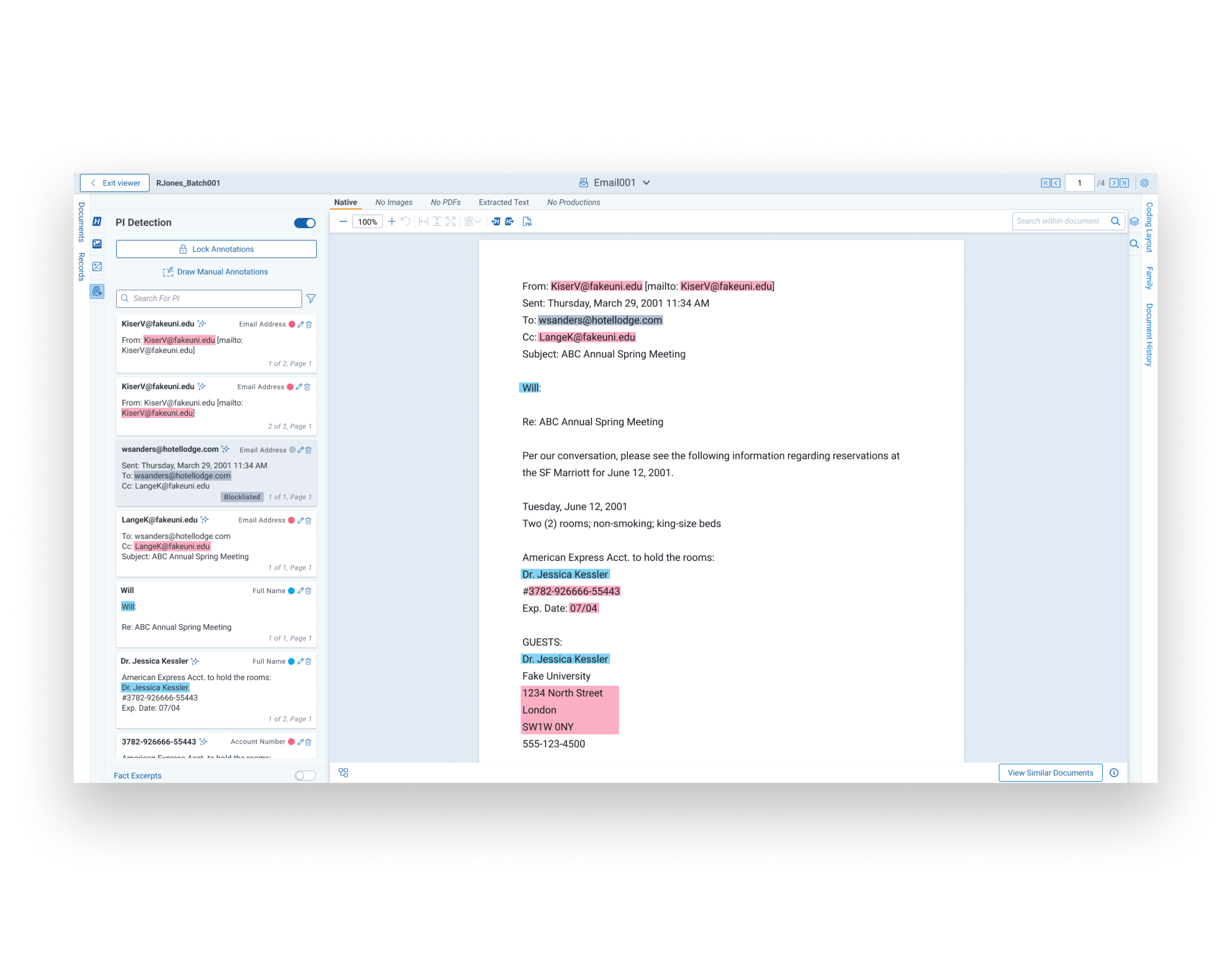
Review and normalize entities
Resolve conflicts, deduplicate results, and validate impacted-individual profiles before export.
Get notification-ready outputs
Generate entity reports and reviewable downstream outputs with fewer revalidation loops.
Bring Breach Response into One Platform
See how aiR for Data Breach Response helps you move from incident data to defensible outputs – fast.
Learn more about aiR for Data Breach Response
Introducing Relativity aiR for Data Breach Response
Read about our approach to cyber incident response from Relativity Chief Product Officer Chris Brown.
Read the Blog PostPreparing for the Inevitable: AI-Driven Incident Response
See the benefits and quantitative results of using AI for your response versus the traditional and outdated approaches.
Read the White PaperIs It Unethical Not to Use AI?
The risks of integrating AI into the practice of law are important to consider, but there's another important question to answer: Could it be unethical not to use AI?
Read the Blog Post